Executive Summary

Scattered Spider, also referred to as UNC3944, Scatter Swine, Muddled Libra, and Roasted 0ktapus, is a financially motivated threat actor group that has been active since May 2022. Scattered Spider has largely been observed targeting telecommunications and Business Process Outsourcing (BPO) organizations. However, recent activity indicates that this group has started targeting other sectors, including critical infrastructure organizations.
Despite this change in targets, Scattered Spider continues to leverage a variety of social engineering tactics, including Telegram and SMS phishing, SIM swapping, MFA fatigue, and other tactics as part of their attacks. This group has often been observed impersonating IT personnel to convince individuals to share their credentials or grant remote access to their computers, has been linked to several past phishing campaigns and deployments malicious kernel drivers – including the use of a signed but malicious version of the Windows Intel Ethernet diagnostics driver.
This blog takes a deep dive into the modus operandi of Scattered Spider; the recent events and tools leveraged by the threat actor, vulnerabilities exploited, and their impact. Additionally, the MITRE ATT&CK Techniques/Sub-Techniques and their mitigations. Finally, the known associated indicators of compromise that can be used to implement detection, prevention, and response strategies.
Recent Events
Scattered Spider typically exploits vulnerabilities such as CVE-2015-2291 and utilize tools like STONESTOP and POORTRY to terminate security software and evade detection. The group demonstrates a deep understanding of the Azure environment and leverages built-in tools for their attacks. Once initial access has been gained, Scattered Spider has been observed conducting reconnaissance of various environments, including Windows, Linux, Google Workspace, Azure Active Directory, Microsoft 365, and AWS, as well as conducting lateral movement and downloading additional tools to exfiltrate VPN and MFA enrollment data in select cases. The group has also been known to establish persistence through legitimate remote access tools such as AnyDesk, LogMeIn, and ConnectWise Control.
By January 2023, Scattered Spider was involved in more than half a dozen incidents from mid-2022 through early 2023 where large outsourcing firms serving high-value cryptocurrency institutions and individuals were targeted.
In December 2022, Scattered Spider conducted campaigns targeting telecom and BPO organizations. The objective of the campaign appeared to be to gain access to mobile carrier networks and, as evidenced in two investigations, perform SIM swapping activity. Initial access was varied: Social engineering using phone calls and text messages to impersonate IT personnel, and either directing victims to a credential harvesting site or directing victims to run commercial Remote Monitoring and Management (RMM) tools. The campaigns were extremely persistent and brazen. Once the adversary was contained or operations are disrupted, they immediately moved to target other organizations within the telecom and BPO sectors.
In the same month, their use of attestation signing to sign malware was discovered. Microsoft disclosed the steps they took to implement blocking protections and suspend accounts that were used to publish malicious drivers that were certified by its Windows Hardware Developer Program. The problem was initiated after Microsoft was notified of rogue drivers being used in post-exploitation efforts, including deploying ransomware.
In August 2022, Twilio identified unauthorized access to information related to 163 Twilio customers, including Okta. Mobile phone numbers and associated SMS messages containing one-time passwords were accessible to Scattered Spider via the Twilio console. The phishing kit used by the threat actor was designed to capture usernames, passwords, and OTP factors and targeted technology companies, telecommunications providers and organizations and individuals linked to cryptocurrency.
Tools
Scattered Spider uses POORTRY and STONESTOP to terminate security software and evade detection.
- POORTRY is a malicious driver used to terminate selected processes on Windows systems, e.g., Endpoint Detection and Response (EDR) agent on an endpoint. To evade detection, attackers have signed POORTRY driver with a Microsoft Windows Hardware Compatibility Authenticode signature.
- STONESTOP is a Windows userland utility that attempts to terminate processes by creating and loading a malicious driver. It functions as both a loader/installer for POORTRY, as well as an orchestrator to instruct the driver with what actions to perform.
In April 2023, ALPHV (BlackCat) ransomware group used an updated version of POORTRY to compromise the US payments giant NCR, leading to an outage on its Aloha point of sale platform.,
Vulnerability Exploits
Scattered Spider is known to exploit CVE-2015-2291 which is a vulnerability in the Intel Ethernet diagnostics driver for Windows (iqvw64.sys) that allows local users to cause a denial of service or possibly execute arbitrary code with kernel privileges via a crafted (a) 0x80862013, (b) 0x8086200B, (c) 0x8086200F, or (d) 0x80862007 IOCTL call. Scattered Spider exploited CVE-2015-2291 to deploy a malicious kernel driver in the Intel Ethernet diagnostics driver for Windows (iqvw64.sys).
Additionally, Scattered Spider has exploited CVE-2021-35464 which is a flaw in the ForgeRock AM server. ForgeRock AM server versions before 7.0 have a Java deserialization vulnerability in the jato.pageSession parameter on multiple pages. The exploitation does not require authentication, and remote code execution can be triggered by sending a single crafted /ccversion/* request to the server. The vulnerability exists due to the usage of Sun ONE Application Framework (JATO) found in versions of Java 8 or earlier. Scattered Spider exploited CVE-2021-35464 to run code and elevate their privileges over the Apache Tomcat user on an AWS instance. This was achieved by requesting and assuming the permissions of an instance role using a compromised AWS token.
Impact
Scattered Spider is known for theft of sensitive data and leveraging trusted organizational infrastructure for follow-on attacks on downstream customers.
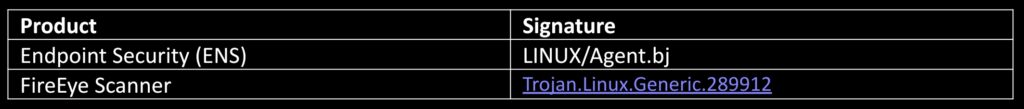
Trellix Product Coverage
Trellix Endpoint, Network, and Email Security offers a multi-layered detection strategy for Scattered Spider activities including checks on the IOCs and behavioral analysis to ensure that any potential threat is discovered and stopped from doing harm to our customers. To stay ahead of new and evolving threats, our products continuously monitor and update their threat intelligence databases. That includes the Trellix Multi-Vector Virtual Execution Engine, a new anti-malware core engine, machine-learning behavior classification and AI correlation engines, real-time threat intelligence from the Trellix Dynamic Threat Intelligence (DTI) Cloud, and defenses across the entire attack lifecycle to keep your organization safer and more resilient.
Trellix Protection
MITRE ATT&CK Techniques/Sub Techniques
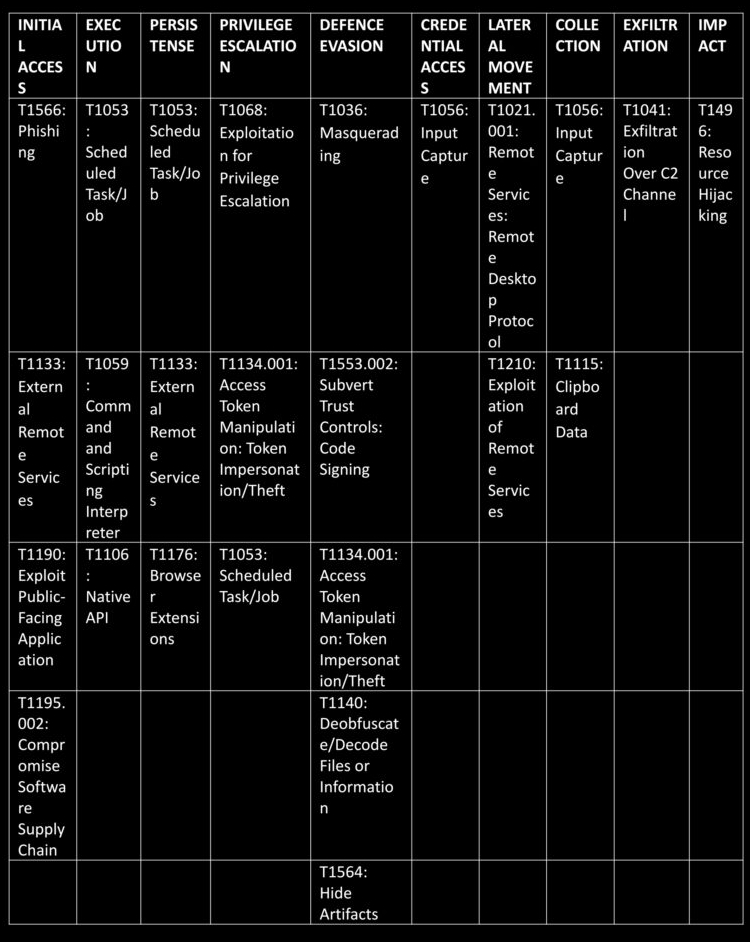
MITRE ATT&CK ENTERPRISE
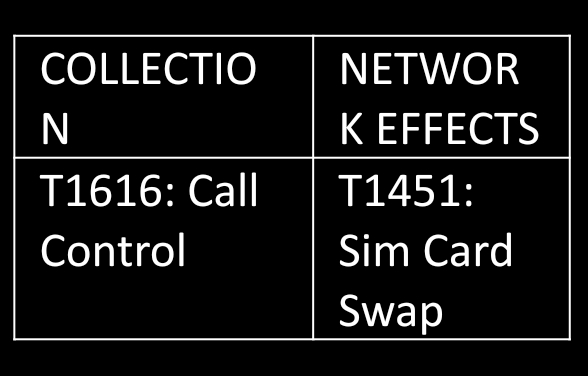
MITRE ATT&CK MOBILE
Mitigations
- M1051: Update software:
Update software regularly by employing patch management for internal enterprise endpoints and servers to mitigate exploitation risk.
- M1017: User training.
Train users to be aware of access or manipulation attempts by an adversary to reduce the risk of successful spear phishing, social engineering, and other techniques that involve user interaction.
- M1011: User Guidance:
Users should be instructed to use forms of multifactor authentication not subject to being intercepted by a SIM card swap, where possible. More secure methods include application-based one-time passcodes (such as Google Authenticator), hardware tokens, and biometrics. Additionally, users should be encouraged to be very careful with what applications they grant phone call-based permissions to. Further, users should not change their default call handler to applications they do not recognize.
- M1049: Antivirus/Antimalware
Anti-virus can be used to automatically quarantine suspicious files.
- M1040: Behavior Prevention on Endpoint
Implement security controls on the endpoint, such as a Host Intrusion Prevention System (HIPS), to identify and prevent execution of potentially malicious files (such as those with mismatching file signatures).
- M1045: Code Signing
Require signed binaries and enforce binary and application integrity with digital signature verification to prevent untrusted code from executing.
- M1038: Execution Prevention
Use tools that restrict program execution via application control by attributes other than file name for common operating system utilities that are needed. Additionally, consider blocking the execution of known vulnerable drivers that adversaries may exploit to execute code in kernel mode. Validate driver block rules in audit mode to ensure stability prior to production deployment.
- M1021: Restrict Web-Based Content
Restrict use of certain websites, block downloads/attachments, block JavaScript, restrict browser extensions, etc.
- M1022: Restrict File and Directory Permissions
Use file system access controls to protect folders such as C:\Windows\System32.
- M1042: Disable or Remove Feature or Program
Remove or deny access to unnecessary and potentially vulnerable software to prevent abuse by adversaries.
- M1048: Application Isolation and Sandboxing
Make it difficult for adversaries to advance their operation through exploitation of undiscovered or unpatched vulnerabilities by using sandboxing. Other types of virtualizations and application micro segmentation may also mitigate the impact of some types of exploitation. Risks of additional exploits and weaknesses in these systems may still exist.
- M1031: Network Intrusion Prevention
Use intrusion detection signatures to block traffic at network boundaries.
- M1032: Multi-factor Authentication
Use two or more pieces of evidence to authenticate to a system, such as username and password in addition to a token from a physical smart card or token generator.
- M1050: Exploit Protection
Security applications that look for behavior used during exploitation can be used to mitigate some exploitation behavior. Control flow integrity checking is another way to potentially identify and stop a software exploit from occurring.
- M1019: Threat Intelligence Program
Develop a robust cyber threat intelligence capability to determine what types and levels of threat may use software exploits and 0-days against a particular organization.
- M1026: Privileged Account Management
Limit permissions so that users and user groups cannot create tokens. This setting should be defined for the local system account only. GPO: Computer Configuration > [Policies] > Windows Settings > Security Settings > Local Policies > User Rights Assignment: Create a token object. Also define who can create a process level token to only the local and network service through GPO: Computer Configuration > [Policies] > Windows Settings > Security Settings > Local Policies > User Rights Assignment: Replace a process level token. Administrators should log in as a standard user but run their tools with administrator privileges using the built-in access token manipulation command runas.
- M1018: User Account Management
Restrict users and accounts to the least privileges they require. An adversary must already have administrator level access on the local system to make full use of this technique.
- M1047: Audit
Toolkits like the PowerSploit framework contain PowerUp modules that can be used to explore systems for permission weaknesses in scheduled tasks that could be used to escalate privileges.
- M1028: Operating System Configuration
Configure settings for scheduled tasks to force tasks to run under the context of the authenticated account instead of allowing them to run as SYSTEM. The associated Registry key is located at HKLM\SYSTEM\CurrentControlSet\Control\Lsa\SubmitControl. The setting can be configured through GPO: Computer Configuration > [Policies] > Windows Settings > Security Settings > Local Policies > Security Options: Domain Controller: Allow server operators to schedule tasks, set to disabled.
- M1035: Limit Access to Resource Over Network
Prevent access to file shares, remote access to systems, unnecessary services. Mechanisms to limit access may include use of network concentrators, RDP gateways, etc.
- M1030: Network Segmentation
Architect sections of the network to isolate critical systems, functions, or resources. Use physical and logical segmentation to prevent access to potentially sensitive systems and information. Use a DMZ to contain any internet-facing services that should not be exposed from the internal network. Configure separate virtual private cloud (VPC) instances to isolate critical cloud systems.
- M1033: Limit Software Installation
Block users or groups from installing unapproved software.
- M1016: Vulnerability Scanning
Vulnerability scanning is used to find potentially exploitable software vulnerabilities to remediate them.
- M0810: Out-of-Band Communications Channel
Have alternative methods to support communication requirements during communication failures and data integrity attacks.
- M1057: Data Loss Prevention
Use a data loss prevention (DLP) strategy to categorize sensitive data, identify data formats indicative of personal identifiable information (PII), and restrict exfiltration of sensitive data.