Cybercriminals employing SIM swapping techniques have adapted their tactics to target phone numbers by porting them onto new eSIM cards, which are digital SIMs stored on the chip of smartphones.
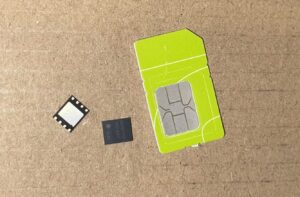
Embedded Subscriber Identity Modules (eSIMs) function similarly to physical SIM cards but can be remotely reprogrammed and provisioned, making them a target for attackers. Users can add an eSIM to their device by scanning a QR code from the service provider, making it a convenient option for cellular connectivity, particularly on devices like wearables.
Russian cybersecurity firm F.A.C.C.T. has observed an increase in SIM swapping attacks leveraging eSIM technology to hijack phone numbers and gain unauthorized access to sensitive accounts, such as online banking services. Attackers exploit the ability to replace or restore a digital SIM card, transferring the victim’s phone number to their own device with an eSIM.
Previously, SIM swappers relied on social engineering or insider assistance from mobile carrier services to port a target’s number. However, as security measures improved, criminals shifted their focus to exploiting vulnerabilities in emerging technologies like eSIMs.
In the latest iteration of these attacks, cybercriminals breach a user’s mobile account using stolen or brute-forced credentials and initiate the porting process themselves. They generate a QR code through the compromised account, which is then used to activate a new eSIM on their device, effectively hijacking the victim’s number. Meanwhile, the legitimate owner’s eSIM/SIM is deactivated.
By gaining control of the victim’s phone number, attackers can intercept access codes and two-factor authentication messages, enabling them to access various online services, including banking and messaging platforms. This access opens the door to a range of fraudulent activities, with online banking services being a primary target.
Moreover, by porting the number to their device, attackers can access SIM-linked accounts on messenger apps, allowing them to impersonate the victim and deceive others into sending money, amplifying the scope of their scams.
To mitigate the risk of eSIM-swapping attacks, experts advise users to employ strong, unique passwords for their cellular service provider accounts and enable two-factor authentication where available. For critical accounts like e-banking and cryptocurrency wallets, additional security measures such as physical keys or authenticator apps are recommended to enhance protection against unauthorized access.
In conclusion, the evolution of SIM swapping techniques to exploit eSIM technology underscores the importance of robust security measures and user vigilance in safeguarding against cyber threats targeting personal information and financial assets.