Netskope Threat Labs has today published its latest research report, focused on cloud threats in the retail sector. The report finds that IoT botnets, remote access tools and infostealers were the key malware families deployed by attackers targeting retail in the past year. Retail has also undergone a shift over the past year from predominantly Google Cloud-based applications towards Microsoft apps like Outlook.
Key findings include:
Attackers using infostealers to target retail: Infostealers are a prominent malware family for the retail sector as attackers attempt to steal valuable data such as payment details from organisations and customers.
Infostealers also feed into the wider cybercrime ecosystem with attackers selling harvested credentials and personal financial details.
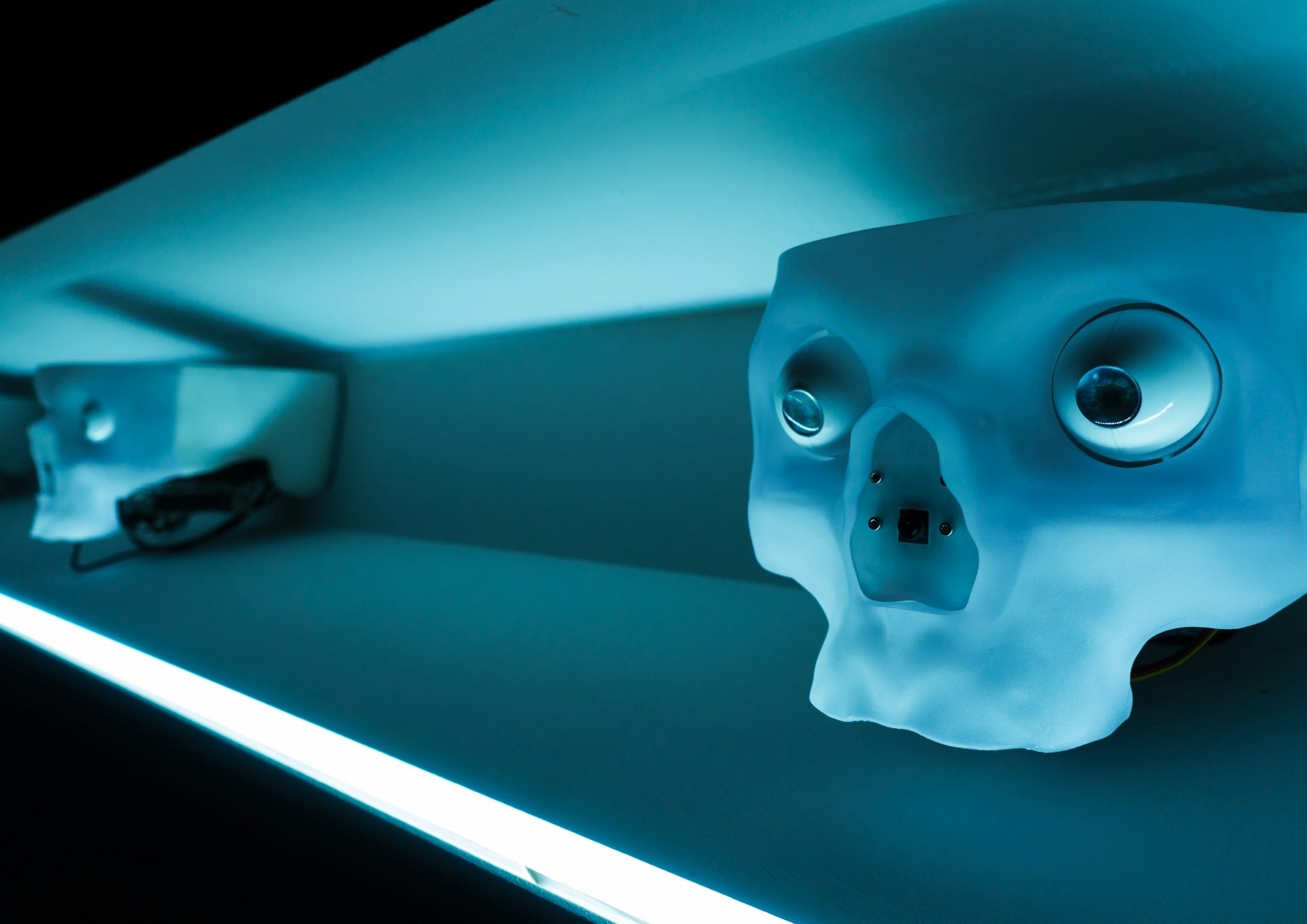
Botnets and trojans targeting network devices: The Mirai botnet family has increasingly been seen to target exposed networking devices running Linux such as routers, cameras, and other IoT devices in the retail environment
IoT devices are often overlooked as a security risk, but can be effective in providing visual or sensor information that can assist in cybercrime, or even abused to launch DDoS attacks against other targets.
Similarly, remote access trojans (RAT) were popular as they allow access to browsers and remote cameras, sending information to attackers or receiving commands.
Since the leak of Mirai malware’s source code, the number of variants of this malware has increased considerably and poses a risk to retail as a sector with multiple vulnerable endpoints.
Microsoft Suite increasingly a target: In last year’s report, Google applications were far more popular in the retail sector than in other industries, but over the past year the researchers have seen a resurgence of Microsoft’s popularity. This is particularly evident for storage with the gap between OneDrive and Google Drive widening over the past year, with the average percentage of users shifting from 43% to 51% for OneDrive and falling from 34% to 23% for Google Drive. We see similar trends with Outlook (21%) supplanting Gmail (13%) as the most popular email app.
Microsoft OneDrive remains the most popular cloud application for malware delivery across all sectors including retail. Attackers gravitate towards tactics that capitalise on users’ trust and familiarity with OneDrive, increasing the likelihood they will click on the links and download the malware.
In retail, attacks via Outlook are more successful than in other sectors – retail sees twice as many malware downloads via Outlook (10%) as other industry averages (5%).
WhatsApp’s popularity in retail: The app was three times as popular in retail (14%) than other industries (5.8%) both for average usage and downloads. However, WhatsApp was not listed among the current top apps for malware downloads. This may change as threat actors start to see its popularity justifying the economic case to direct more attacks via the app.
Social media applications like X (12%), Facebook (10%) and Instagram (1.5% for uploads) were all more popular in retail than other industry averages.
Speaking on the findings, Paolo Passeri, Cyber Intelligence Principal at Netskope said;
“It’s surprising that the retail sector still finds itself specifically targeted with botnets like Mirai as attackers look to compromise vulnerable or misconfigured IoT devices across retail locations and abuse them to dramatically amplify the effect of a Distributed Denial of Service (DDoS) attack. Mirai is not a particularly recent threat, and since its discovery in 2016, there are now multiple variants used today. The fact that attackers continue to use it to target IoT devices shows that too many organisations continue to dangerously overlook the security posture of their internet-connected devices. This poses a significant risk not only for the targets of the attacks launched from the IoT botnet but also for the organisation whose IoT devices are enslaved into the botnet, since their exploitation can easily lead to outages that impact the functioning of the business.
“This vulnerability, coupled with the use of infostealers and remote access malware to extract credentials and customer financial data makes the retail sector a potentially lucrative target.
“I was particularly interested to see that Qakbot is among the top threats for retailers, even though this operation was taken down by the FBI at the end of August 2023. Its infrastructure has been quickly refitted by the attackers to distribute additional malware payloads, providing additional opportunities for the attackers; and some isolated Qakbot campaigns have been detected even after its disruption.
“The fact that botnets like Mirai and infostealers like Quakbot continue to be among the top methods attackers use to target retail organisations shows security leaders still have much to do to fortify their infrastructure and endpoints. Fortunately, following fundamental cyber hygiene best practices like inspecting web and cloud traffic and ensuring you can block malicious traffic and isolate compromised endpoints or domains will reduce the risk that you fall victim to these attackers.”
Netskope Threat Labs recommends enterprises in the retail sector review their security posture and make several recommendations for best practices to counter these threats:
Inspect all HTTP and HTTPS downloads, including all web and cloud traffic, to prevent malware from infiltrating your network.
Ensure that high-risk file types like executables and archives are thoroughly inspected using a combination of static and dynamic analysis before being downloaded.
Configure policies to block downloads and uploads from apps and instances that are not used in your organisation to reduce your risk surface to only those apps and instances that are necessary for the business and minimise the risk of accidental or deliberate data exposure from insiders or abuse by attackers.
Use an Intrusion Prevention System (IPS) that can identify and block malicious traffic patterns, such as command and control traffic associated with popular malware. Blocking this type of communication can prevent further damage by limiting the attacker’s ability to perform additional actions.
Use Remote Browser Isolation (RBI) technology to provide additional protection when there is a need to visit websites that fall into categories that can present higher risk, like newly observed and newly registered domains.
The report is based on anonymised usage data collected about a retail sector subset of Netskope’s 2,500+ customers, all of whom give prior authorisation for their data to be analysed in this manner.