The Acronis Cyber Threats Update covers current cyberthreat activity and trends, as observed by Acronis analysts and sensors. Figures presented here were gathered in August of this year and reflect threats that we detected as well as news stories from the public domain. This report represents a global outlook and is based on over one million unique endpoints distributed around the world.
The top five numbers for this report:
- 7.1 million malicious URLs were blocked at the endpoint by Acronis in August 2023. That’s a decrease of 55% compared to July, but 1% more than in August of 2022.
- Acronis detected 42,890 endpoints with malware attacks in August — a 16% increase compared to July.
- Ransomware detections at the endpoint increased 3% from July to August. The most active ransomware group in August was LockBit, claiming 126 victims.
- In August, the Endpoint Detection and Response (EDR) pack for Acronis Cyber Protect Cloud detected more than 225,000 incidents — a majority of which were automatically remediated.
- We recorded almost 379 data breaches that were reported globally.
Incidents of the month
Data breaches remain a widespread nuisance affecting millions of users. In August, for example, a data breach at Discord.io exposed the information of 760,000 members, including hashed passwords. This data has already been made available for purchase on an underground forum.
Another recent data breach impacted Pôle emploi, the French unemployment registration and financial aid agency. Data belonging to an estimated 10 million citizens was exposed. Luckily, this did not include email, password or banking credentials. Nevertheless, the data is still useful for cybercriminals, and such information is often used to personalize future social engineering email campaigns.
The most common causes behind data breaches are double-extortion ransomware, SQL injections and information-stealing Trojans. One of the more common infostealers, Raccoon Stealer, announced a new version (2.3.0) in August. This new version is stealthier and attempts to prevent researchers from finding their online dashboard, while it steals credentials from 60 different applications. Raccoon Stealer is distributed under the malware-as-a-service (MaaS) model and is currently being sold for $200 per month.
With so many avenues available for cybercriminals to attack data, the importance of robust data protection is paramount.
Ransomware detections
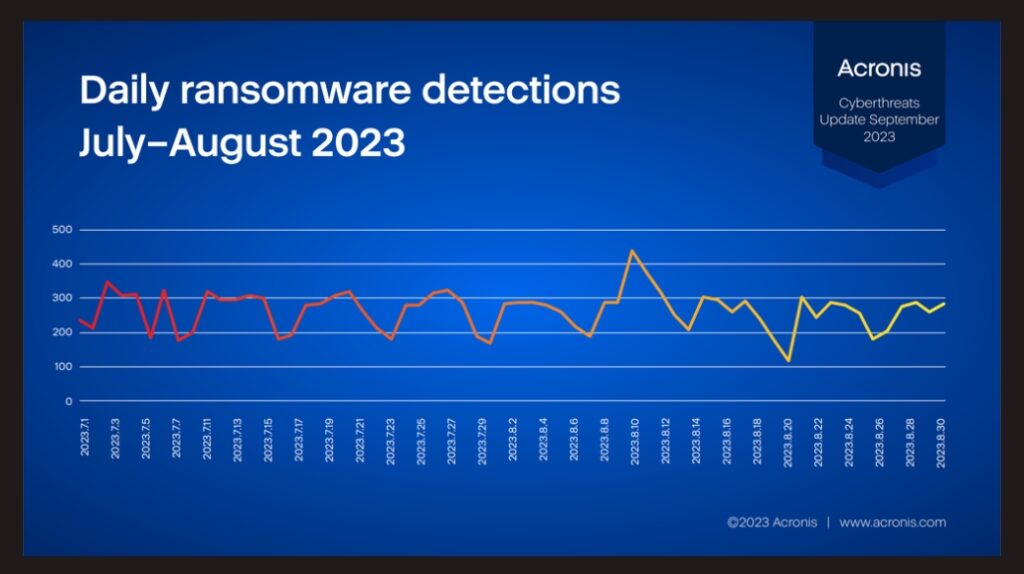
Ransomware detections in August increased 3% compared to July 2023. The day with the most ransomware detections was August 9, when 438 encryption attempts were blocked.
The statistics presented here are taken from Acronis’ anti-ransomware heuristics, which detect encryption attempts on any workload. This represents the last line of defense in the protection layer. Threats that reached this stage were able to penetrate or disable all previous layers of protection, such as email filters and static antivirus detection processes. The actual number of attempted ransomware attacks will thus be higher.
Daily ransomware detections, July–August 2023
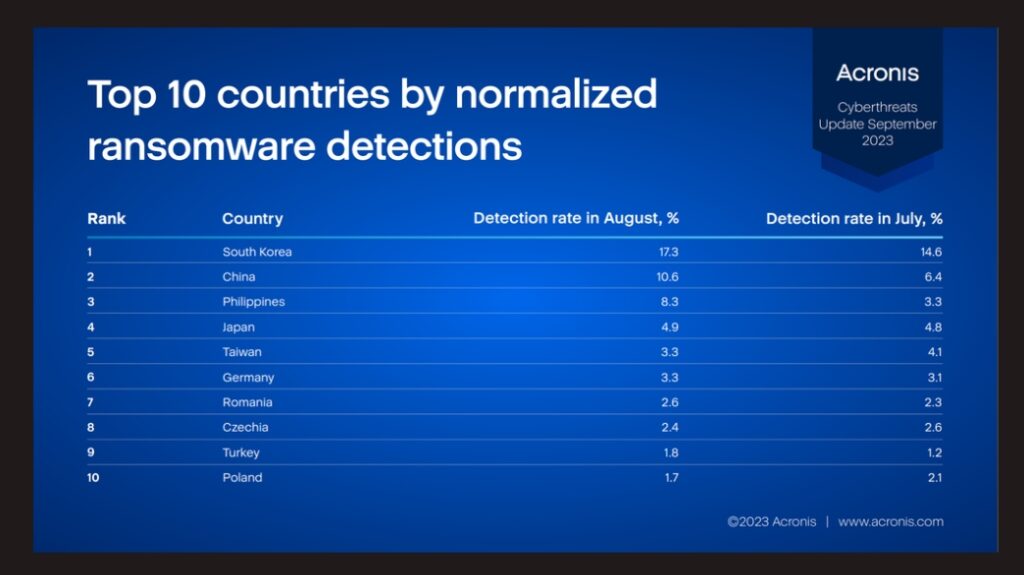
The following table shows the normalized percentage of clients with at least one ransomware detection in the given month. The higher the number, the higher the risk of a workload in that country being attacked by ransomware.
Top 10 countries by normalized ransomware detections
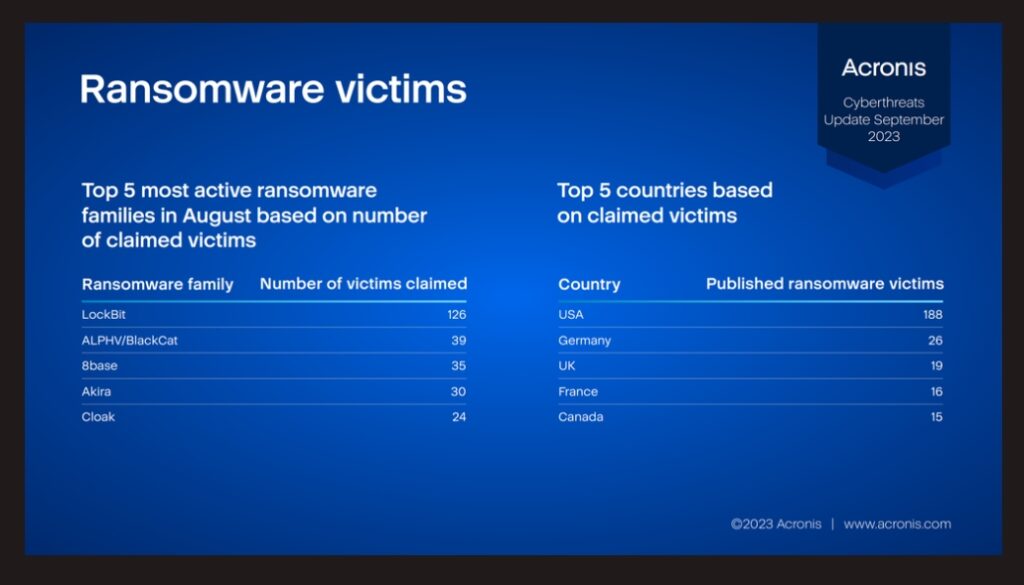
The following statistics are based on data from darknet websites, where ransomware groups publish reports about their victims and release stolen files. These figures may change slightly over time, as not all ransomware groups announce their successes immediately, and some keep victims’ names private while ransom negotiations are ongoing. These numbers represent the view from the ransomware groups’ side, which differs from the detection numbers listed above.
Top 5 most active ransomware families by number of claimed victims, and the top 5 countries by number of claimed victims, August 2023
Protection
The aforementioned threats can be detected and mitigated with solutions from Acronis.
Acronis Cyber Protect protects against both known and never-before-seen threats through a multilayered protection approach. This includes behavior-based detection, AI- / ML-trained detections, and anti-ransomware heuristics, which can detect and block encryption attempts and roll back any tampered files automatically, without any user interaction.
The Endpoint Detection and Response (EDR) pack for Acronis Cyber Protect Cloud brings the visibility needed to understand attacks, while simplifying the context for administrators and enabling efficient remediation of any threats.







